1.7 KiB
1.7 KiB
Azure Authentication ✔️
For the Azure Resource Manager the fastest way to get started is by having access to the azure-cli tool. We only need this once.
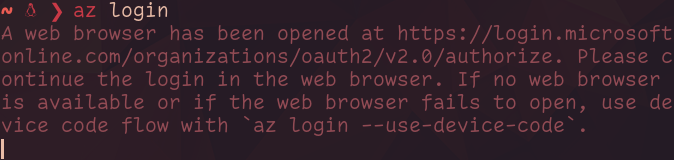
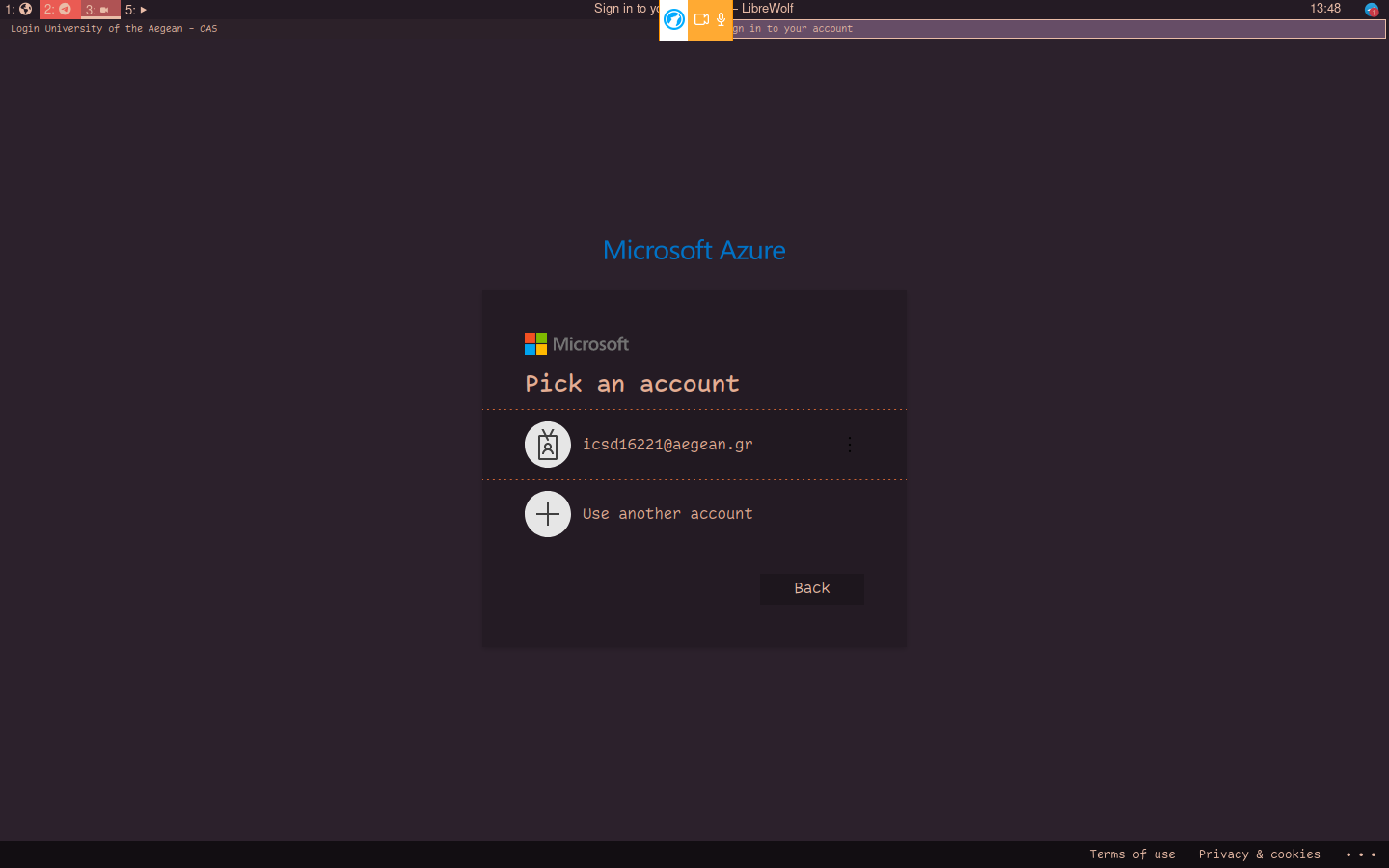
- Execute
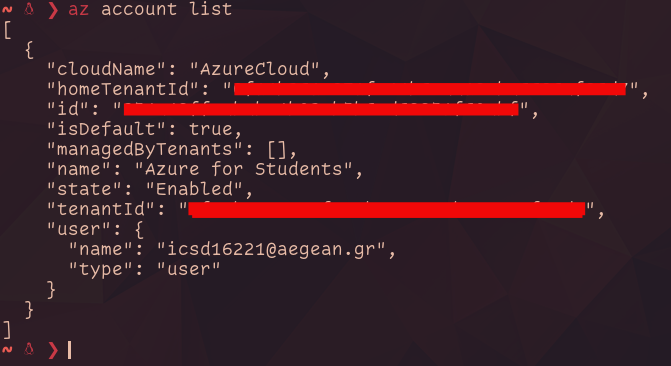
az loginand follow the instructions to log in using a browser.
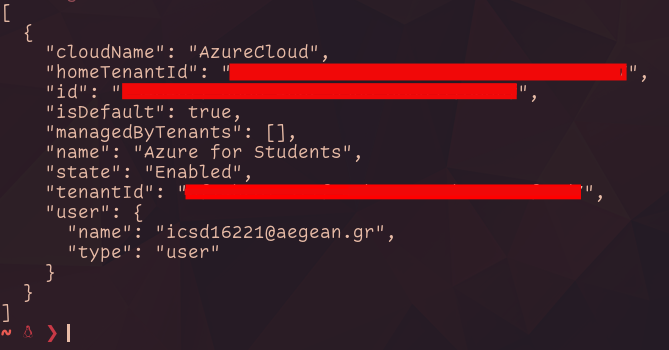
- From the output of the command, take note of the tentantId value.
- After running
az account listtake note of the id value.
-
Create a new application with
az ad app create --display-name "AppName" -
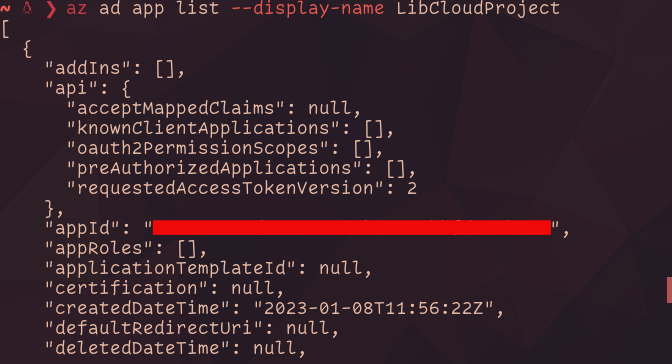
With
az ad app list --display-name AppNametake note of the appId
-
Create a new service principal with
az ad sp create --id appId -
Get an id value from
az ad sp list --display-name AppNameto create a new role withaz role assignment create --assignee "id we got just now" --role Owner --scope /subscriptions/sub id we got
- Head over to https://portal.azure.com/#view/Microsoft_AAD_RegisteredApps/ApplicationMenuBlade/~/Credentials/appId/appId we got/defaultBlade/AppRoles and create a new client secret to be used in for the authentication.
The values we need translate to the following:
- AZURE_TENANT_ID -> tentantId
- AZURE_SUB_ID -> id from step 3
- AZURE_APP_ID -> appId
- AZURE_PASSWORD -> value of the secret we added
Note: Make sure your subscription is registered to use at least Microsoft.Compute and Microsoft.Network. From the subscriptions page and resource providers tab.